Banks and Financial Institutions
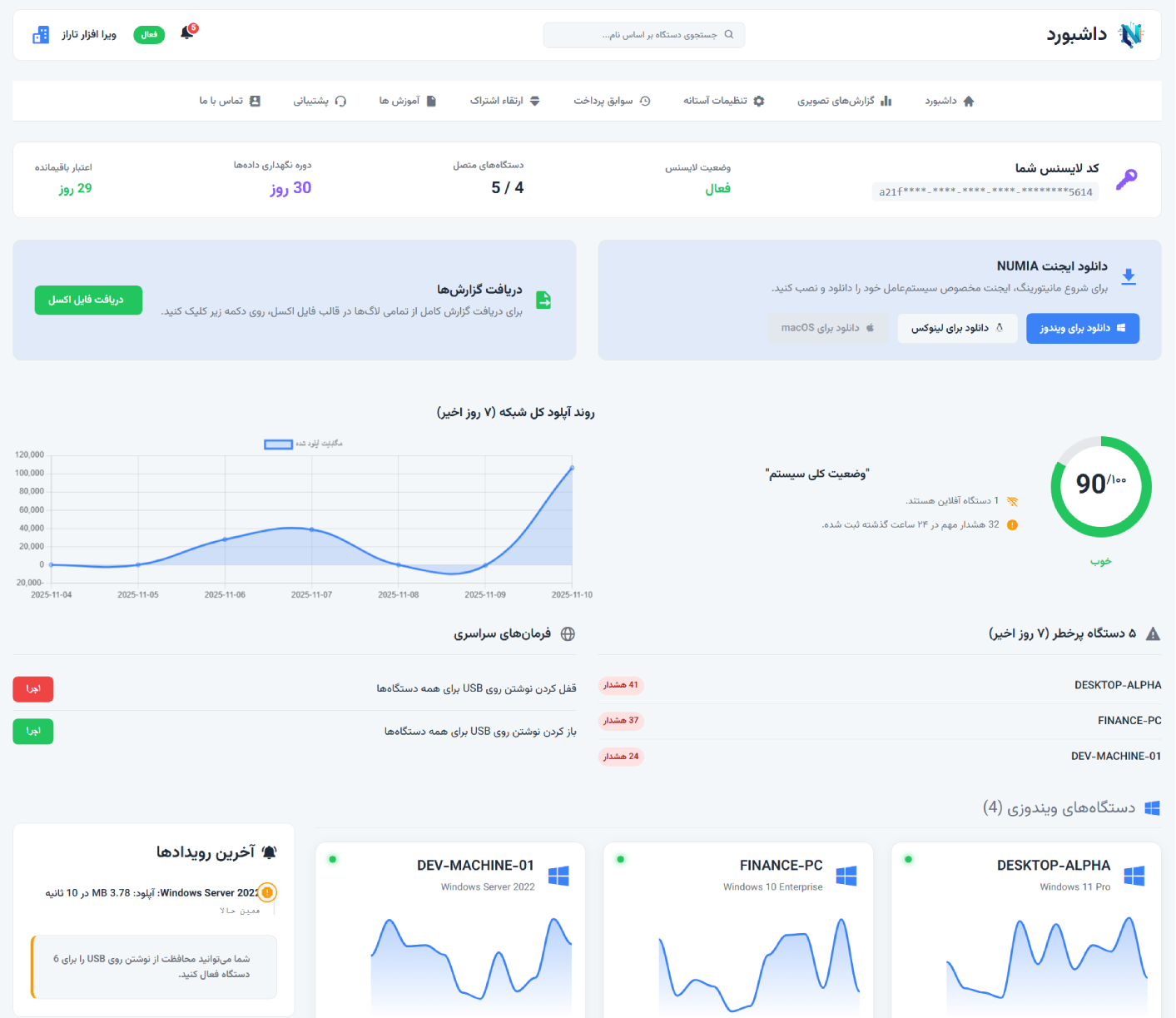
Protecting sensitive customer data and fully complying with legal and regulatory requirements.
- Protection of account and transaction information
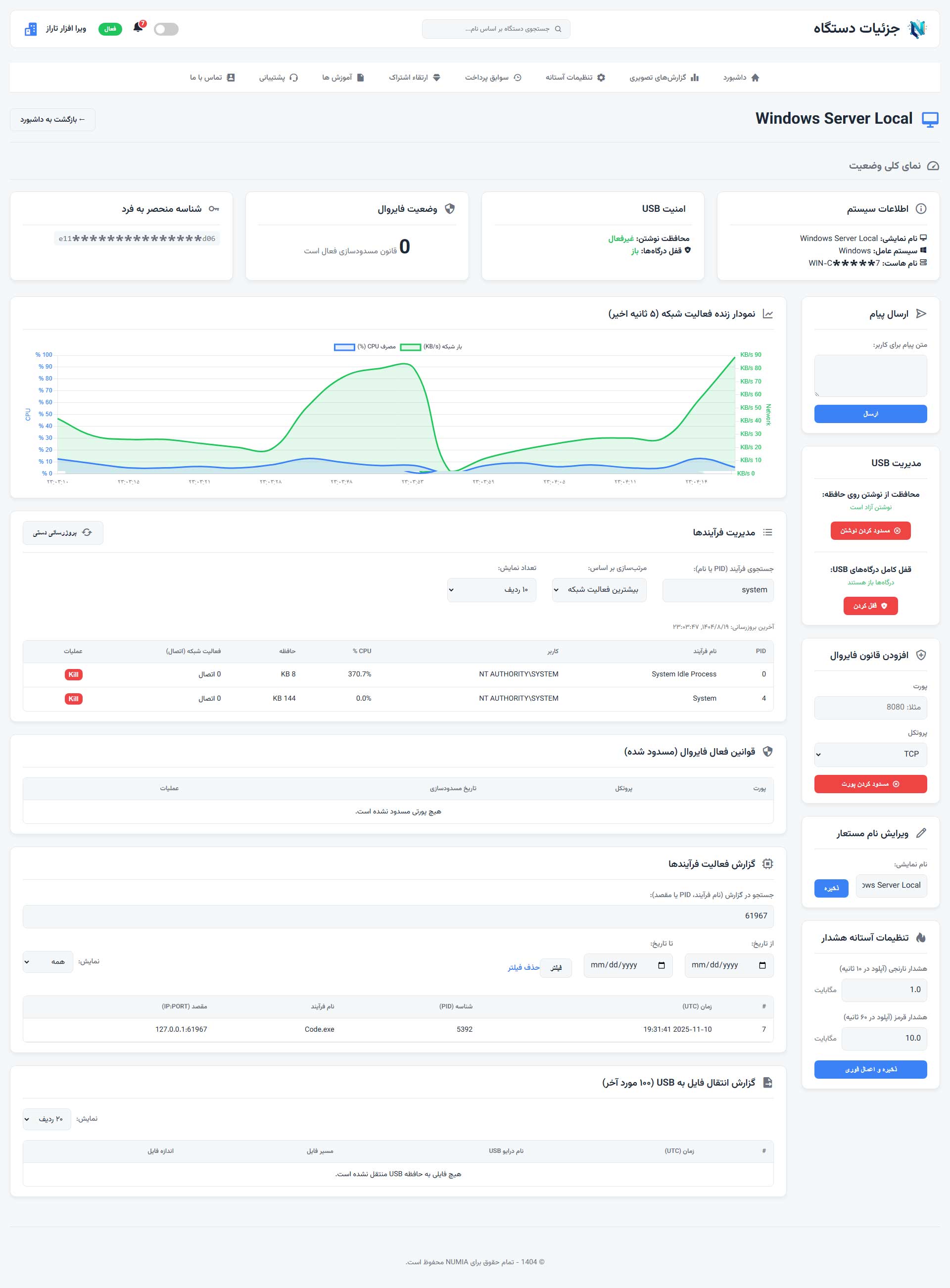
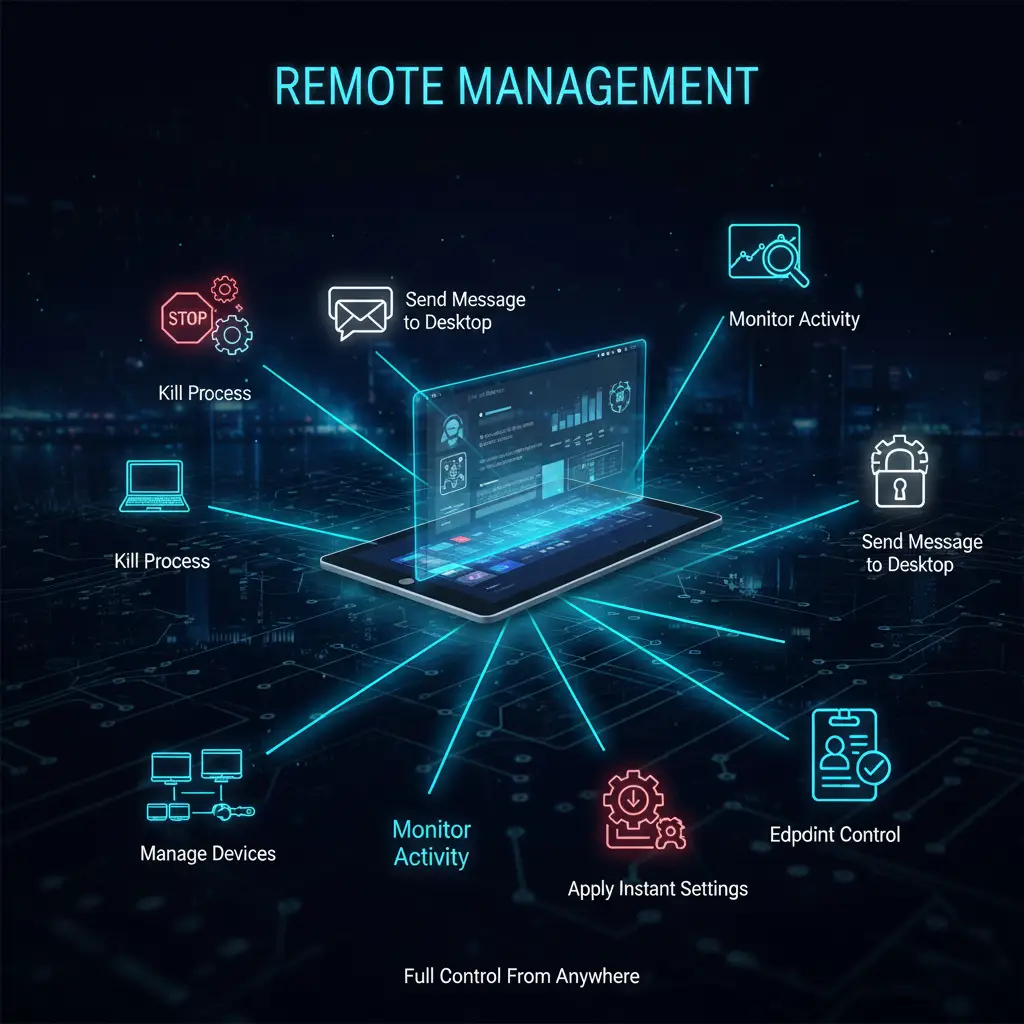
- Countering Insider Threats
- Full control over employee access to data
- Meeting Central Bank compliance requirements